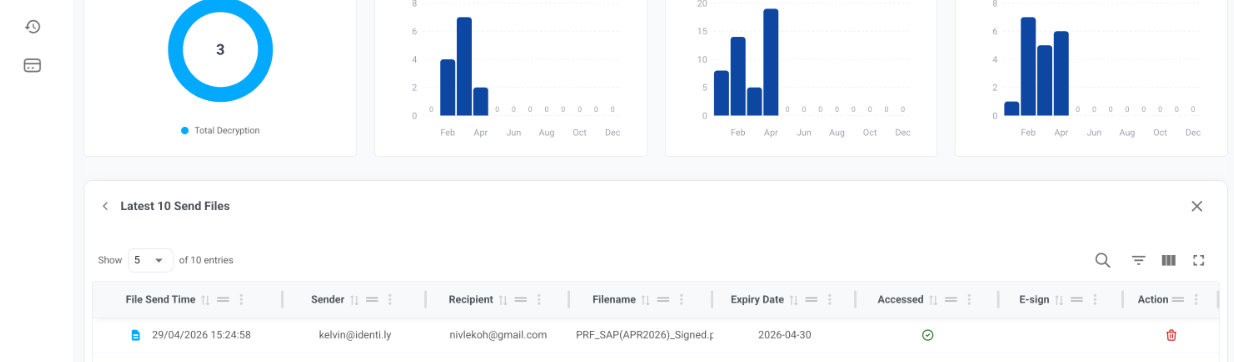
Ensure sensitive documents only reach the intended recipient.
Identity-verified access and signing powered by our proprietary FaceKey™ or through government-trusted identities, such as Singpass™ — not passwords, links, or blind trust.
Trusted by leading enterprises for secure document sharing